Nemo Protocol released a comprehensive post-mortem blaming a rogue developer for deploying unaudited code containing critical vulnerabilities that enabled a $2.59 million exploit on September 7.
The DeFi yield platform detailed how the unnamed developer secretly introduced new features without audit approval and used unauthorized smart contract versions.
The attack exploited two key vulnerabilities: a flash loan function incorrectly exposed as public and a query function that could modify contract state without authorization.
Hackers bridged stolen funds to Ethereum via Wormhole CCTP, with $2.4 million currently held in the hacker’s address.
How it All Started
The root cause traces to January 2025, when a developer submitted code containing unaudited features to MoveBit auditors.
The developer failed to highlight new additions while mixing previously audited fixes with unreviewed functionality.
MoveBit issued its final audit report based on incomplete information. The same developer then deployed contract version 0xcf34 using single-signature address 0xf55c rather than the audit-confirmed hash, bypassing internal review processes.
Asymptotic team identified the critical C-2 vulnerability in August, warning that some functions could modify code without permission.
The developer dismissed the severity and failed to implement necessary fixes despite available support.
Attack execution began at 16:00 UTC on September 7 with hackers leveraging the flash loan function and the get_sy_amount_in_for_exact_py_out query vulnerability.
The team detected anomalies thirty minutes later when YT yields displayed over 30x returns.
The Developer’s Secret Code Deployment
In late 2024, initial audit submissions correctly configured flash_loan as an internal non-callable function while development teams iterated on features.
The developer drew inspiration from Aave and Uniswap protocols to maximize composability through flash loan capabilities.
However, the implementation critically underestimated security risks and incorrectly used public methods rather than internal functions.
The earlier-mentioned function, intended to enhance swap quoting mechanisms, contained implementation errors.
Functions designed for read-only purposes were coded with write capabilities, creating the primary attack vector.
On January 5, 2025, the developer integrated unaudited features into the final codebase after receiving MoveBit’s initial audit report.
The mixed version contained both fixed issues and new unaudited features without explicit scope highlighting.
The developer communicated directly with the MoveBit team on January 6, obtaining final audit reports through modification of previous versions.
Instead of using confirmation hashes from audit reports, separate upgrades and deployments occurred without the internal team’s knowledge.
Single-signature deployment address enabled unauthorized contract version activation. This version remained in the active code until exploit occurrence despite subsequent security procedure implementations.
April’s transition to multi-signature upgrade protocols failed to address the fundamental issue.
The developer transferred only contract caps while maintaining vulnerable code rather than deploying audit-confirmed versions.
Fund Recovery and Security Remediation Efforts
Stolen assets totaling $2.59 million were quickly moved through sophisticated laundering operations.
Primary attacker wallet initiated cross-chain transfers at 16:10 UTC via Wormhole CCTP before final aggregation on Ethereum.
However, security teams established monitoring protocols for the holding address while coordinating with centralized exchanges on asset freezing.
White-hat agreement frameworks and hacker bounty programs were also implemented to encourage fund recovery.
As for the remediation effort, emergency incremental audits were submitted to Asymptotic with plans for additional independent security firm reviews.
Manual-fix functions were also integrated into new contract patches to enable multi-signature wallet restoration of corrupted code.
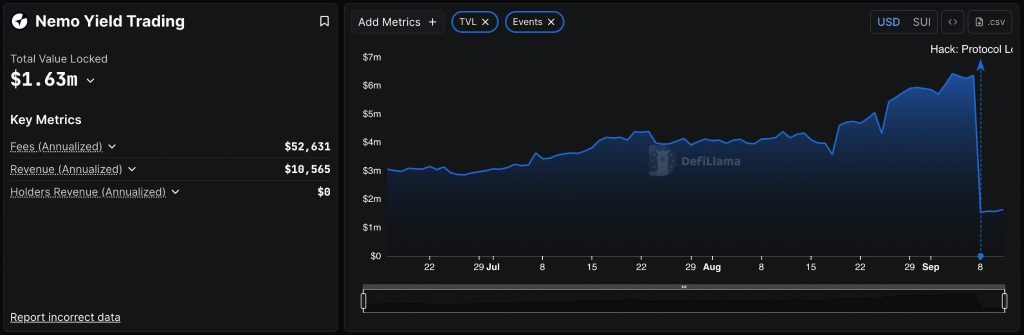
As a result of the hack, the total value locked instantly collapsed from $6.3 million to $1.63 million now as users withdrew over $3.8 million worth of USDC and SUI tokens.
To compensate affected users, plans have been put in place for debt-structuring design at the tokenomics level, with community sharing scheduled upon finalization.
The protocol apologized for security failures while implementing enhanced monitoring, stricter controls, additional audit checkpoints, and expanded bug bounty programs.
The exploit contributes to the ongoing 2025’s devastating DeFi security crisis with over $2.37 billion in losses across 121 incidents in the first half alone.
So far this year, September emerged as particularly destructive with SwissBorg’s $41.5 million SOL hack, npm supply chain attacks affecting billions of downloads, and multiple protocol exploits happening almost at the same time.
The post Nemo Protocol Blames $2.6M Exploit on Developer Who Deployed Unaudited Code appeared first on Cryptonews.


 Nemo Protocol loses $2.4M to hackers on Sui blockchain as TVL crashes 75% from $6.3M, marking the third major DeFi hack this month alone.
Nemo Protocol loses $2.4M to hackers on Sui blockchain as TVL crashes 75% from $6.3M, marking the third major DeFi hack this month alone.